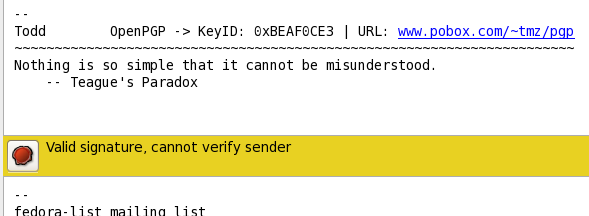
Tim: >> John Doe <johndoe@xxxxxxxxxxx> creates his own key, signs his messages, >> publishes his key. You receive his message, you check the key, it's >> confirmed. Todd Zullinger: > Part of checking the key includes verifying the key id and > fingerprint. After verifying this info I would sign the key to make > it valid. (A signature can be marked as non-exportable, for keys you > want to sign but don't want your signature to be exported along with > that key if you sent it to someone else.) > > With a signature from my trusted key on John Doe's key, gpg now treats > this key as valid. Of course, but the *problem* is that, often, actual *verification* isn't possible. It's someone on the other side of the world, etc. So, the reality is that most signatures stay as *unverified*, with the few that aren't, being labelled as verified when they're really not. > I use mutt and I see the gpg output directly. I've played around with > thunderbird and kmail to help friends and both have indicators for > this sort of thing. I'd be a little surprised it evolution doesn't > handle it in some way as well. It does something similar. A whacking great big coloured bar across the bottom of the page. Bright yellow if the signature matches the message, but isn't verified. Green if both check out. Red if some aspect fails. And in that bar is a clickable icon for you to get a wordy description (what I pasted, previously). (A screenshot of the bar has been attached.) > This is all not that different from signatures on paper. If I sign a > document as John Doe and you trust it without any other verification > that I am the John Doe you wish to do business with, you can be easily > fooled. I know. And that's the usual way it's used. Blind faith. >> There really is nothing that either person can do to invalidate the >> other key. It'd take a war of words between the two people in a >> common forum for someone else to tell them apart. Even then, some >> will believe they're the same person, just playing at trolling >> games. It's common enough for users to have multiple addresses, and >> they may use separate PGP keys. > No one has to invalidate anyone else's key. Well, in the sense of making it apparent that someone is forging things. The blind faith aspect of using PGP, in the absense of other information, is one of its Achille's heels. > I sign my messages with a key that has the following properties: > > pub 2048R/BEAF0CE3 2006-07-04 > Key fingerprint = 2067 23CE 8C4A 9D39 9FFF B8E7 4325 938B BEAF 0CE3 > uid Todd M. Zullinger <tmz@xxxxxxxxx> > sub 4096R/8550ADF3 2006-07-04 [expires: 2012-12-21] > > Import and sign that key on your keyring (--lsign-key in gpg). Then, > in another user account, generate a key with the same user id. Export > this key to a file somewhere and then import it to your normal users > keyring (otherwise you'll have the secret key in your keyring and thus > the key will also be marked as valid, which will make the effects of > the test less visible to you). > > Send yourself a message signed by this fake key from the user account you > generated the key in, and check it in your mail client as your normal > user. You should notice right away that the message isn't signed by a > valid key. That wasn't the faking condition that I was describing. >> In the past I've submitted keys to keyserver, and that's included >> two different keys that include a common e-mail address. A mail >> client wanting a key would be asking for the key by ID not e-mail >> address. It'll get the key that matches the message they're >> checking. > If you're just verifying a signature via a downloaded key which you've > not checked out in any other way, then you'll get the big fat WARNING > like the one above. If you choose to ignore that and trust the signed > message anyway, then that's not a failing of the system, it's a user > failure. (It's a large software failure if that warning doesn't make > it to you in some form.) No, you get the warning that you see with all signed messages. The rather meaningless one. The failing of the system is that it's hard to get a verifiable signature in the first place. i.e. For me to create mine and have it checked so it's meaningful for other people. -- [tim@bigblack ~]$ rm -rfd /*^H^H^H^H^H^H^H^H^H^Huname -ipr 2.6.21-1.3228.fc7 i686 i386 Using FC 4, 5, 6 & 7, plus CentOS 5. Today, it's FC7. Don't send private replies to my address, the mailbox is ignored. I read messages from the public lists.